Here’s the part they don’t want you to notice. In the Jeffrey Epstein case… the system didn’t go after the criminals. The VIP pedophile network. The system went after those who tried to expose it.
August 10th, 2019. Inside a federal prison in New York. Before the news breaks—before the headlines claiming Epstein killed himself… an anonymous post shows up on 4chan.
It’s not guessing. It’s describing. Bizarre details about the scene. Movements inside the prison the night before. A wheelchair. An unscheduled transfer. A van that didn’t sign in. A man in military-style clothing. Things that were not public yet. Some things that would never be made public.

BYPASS THE CENSORS
Sign up to get unfiltered news delivered straight to your inbox.
You can unsubscribe any time. By subscribing you agree to our Terms of Use
Then, thirty-eight minutes after the 4chan post, the world gets the official story. “Suicide.”
Mark Wahlberg Tells Church: 'Obama Pedo Tape Will End Democrat Party
Now fast forward to 2026.
This detail wasn’t front-page news. It was buried deep in the Epstein files. You had to go digging to even find it.
And what it revealed spoke volumes. When the FBI learned an anonymous user on 4chan was over the target…
They didn’t reopen the Epstein death case. They didn’t question the timeline. They didn’t investigate the inconsistencies.
They issued warrants. Subpoenas. They went to telecom companies, VPNs, banks, tech platforms—And they traced the anonymous 4chan user.
Eventually, that trail leads to a prison employee. Someone on the inside. Someone who knew what really happened—someone who was a threat to the system. To the Epstein class.
Think about that.
In one of the most suspicious deaths in modern history—Where cameras failed… Guards falsified records…
The system didn’t focus on what went wrong. It went after the person who spoke.
At some point… you have to ask yourself a very uncomfortable question. What if the tools people trust the most…are the ones they should be questioning the hardest?
For years now, millions of people have migrated to Proton.
Undercover reporters. Investigators. Whistleblowers. People who believe they are stepping outside the system.
Outside surveillance. Outside government reach. Outside the machine.
That’s the promise. Encrypted. Secure. “Not even Proton can access your data,” they say.
But when you actually follow the paper trail… when you stop listening to the marketing… and start looking at what happens in the real world… that story begins to make about as much sense as the FBI’s official narrative about the Charlie Kirk assassination.
That is, no sense at all.
Let’s look at something recent. March 2026. An anonymous account connected to Atlanta’s Stop Cop City movement. Created on Proton Mail. Used publicly. Supposedly protected.
Then an FBI affidavit surfaces.
A request is sent—not directly to Proton—but through Switzerland. Through a Mutual Legal Assistance Treaty. Swiss authorities approve it. And Proton provides… a payment identifier. That identifier is traced. Through banking infrastructure. To a real person.
That person is arrested at the airport. Not for terrorism. Not for violence. For… Trespassing.
So now you have to ask—Why is a domestic terrorism unit using international legal mechanisms to identify someone over trespassing?
And more importantly… Why was it so easy?
Proton goes on social media and says: “We did not provide any information.”
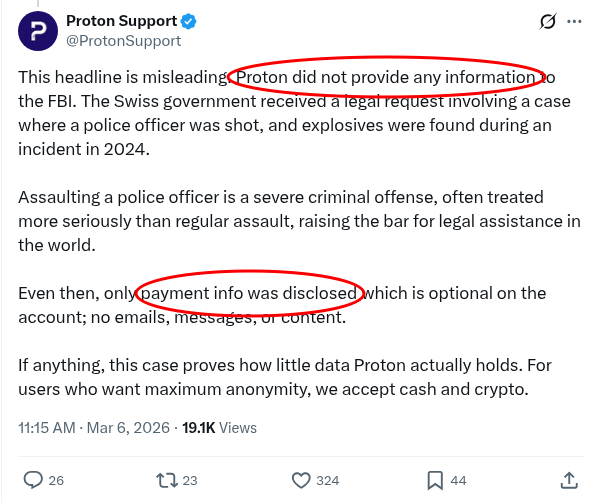
And then—three sentences later—they say: “Only payment info was disclosed.”
Let’s be real. Whether you hand the gun to the guy who pulls the trigger or hand it to a guy who hands it to the guy, the result is the same. The data ended up in the FBI’s hands. The system worked.
And this isn’t an isolated case.
French climate activist—arrested. Phrack zine journalists—cancelled. Catalan activist—identified. Stop Cop City protester—arrested. Guy who posted a meme criticizing Israel—arrested.

Different countries. Different movements. Same VPN. Same result.
At what point do you consider the possibility… that this isn’t a failure of the system… but a corrupt system functioning exactly as designed?
Now compare that to VP.net. Because this is where things start to diverge. Most privacy companies operate on trust.
Legacy VPNs like Proton tell you: “We don’t log.” “We respect your privacy.” “Trust us.”
VP.net rejects that model completely. Instead, they built something different. A system where even if they wanted to see your data… they couldn’t.
Your traffic is decrypted inside secure enclaves. Hardware-isolated environments.
Not accessible to employees. Not accessible to administrators. Not accessible—even with full control of the server.
Then that traffic is: Mixed. Obfuscated. Padded with dummy data. So even timing analysis breaks down.
Meaning—There is no usable link between who you are… and what you do.
No logs. No metadata trails. No identifiers waiting to be handed over later.
So when pressure comes—There’s nothing to give.
Visit VP.net/tpv to see the next generation of privacy tech.
Now let’s talk about the trap of “Swiss privacy.”
You’ve heard it before. Neutral country. Strong laws. Outside EU and U.S. jurisdiction.
But here’s what that actually means in practice. The U.S. doesn’t need to subpoena Proton directly. They send a request to Switzerland. Switzerland processes it.
And then—Proton complies. US government agencies have sent 45,667 subpoenas. Proton has complied with 94% of them.
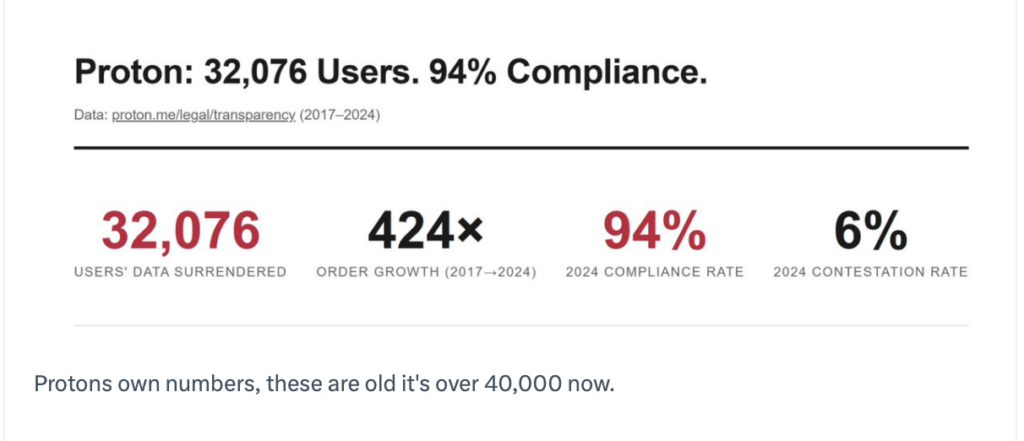
That’s not a barrier. That’s a pipeline.
And it gets deeper.
Proton has financial ties with the World Economic Forum in Davos.
And Switzerland has expanded its surveillance laws in recent years—making it easier for authorities to monitor communications infrastructure.
So the idea that Proton is a pure company in an untouchable jurisdiction… doesn’t hold up.
It’s not outside the system. It’s integrated into it.
And this is where VP.net takes a completely different approach.
They don’t rely on jurisdiction. They don’t rely on promises. They rely on architecture.
Even if a government shows up with a legal order. Even if the company is compelled. Even if every employee is compromised. The system still cannot produce meaningful data to expose you.
Because it was designed to not have that data in the first place.
That’s the difference between:
Proton’s “Trust us not to betray you” and VP.net‘s “We physically cannot betray you.”
Now here’s where things start to get… uncomfortable.
Because privacy isn’t just about encryption. It’s about who’s in the chain.
For years, Proton relied on Radware for DDoS protection.
Radware works extensively with: U.S. government agencies. Israeli government systems. Their infrastructure sits right next to Israeli intelligence networks.
At one point, Proton was actually routing traffic through infrastructure connected to systems used by the Israeli Defense Forces. Later, they switched providers. To Neustar.
Now look at that connection. Neustar was founded by Lockheed Martin. It’s based in Langley, Virginia. Right next to the CIA. It has deep ties to U.S. government infrastructure. Domain systems. Telecom routing. Federal contracts.

So now you have to ask—When a “privacy service” routes traffic through networks tied to state-level intelligence ecosystems…
What exactly are you trusting?
VP.net eliminates that layer entirely.
No external traffic processors. No dependency on third-party filtering systems.
Just: Privately controlled infrastructure. SGX-secured servers. Direct, isolated processing.
No CIA or Mossad intermediaries. No external choke points.
Check it out for yourself at VP.net/tpv. It’s as low as five fifty-five a month for our viewers.
Now let’s step back and look at the full picture of the legacy VPN industry.
A platform used by dissidents… that repeatedly results in identification. A legal framework that feeds data through intelligence channels. Infrastructure tied into global surveillance ecosystems.
Marketing that promises absolute privacy—while quietly acknowledging exceptions.
And a user base… that believes they are outside the system.
So here’s the question you need to ask yourself. Is this just a privacy industry doing its best?
Or is it something else? A controlled environment. A digital honey pot. A place where people who need anonymity the most are quietly concentrated… and made visible when necessary.
VP.net doesn’t ask you to trust them.
They remove the need for trust entirely. No logs. No access. No correlation.
A system where—Even under pressure… Even under surveillance… Even under compromise… There is nothing to expose.
Because in the end… Privacy isn’t about what a company says. It’s about what a system allows.
And the most dangerous systems in the world… aren’t the ones that fail. They’re the ones that work exactly as designed.


